We have made it easy for end-users to come on-board, and easy for management when they leave.
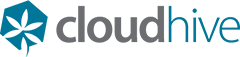
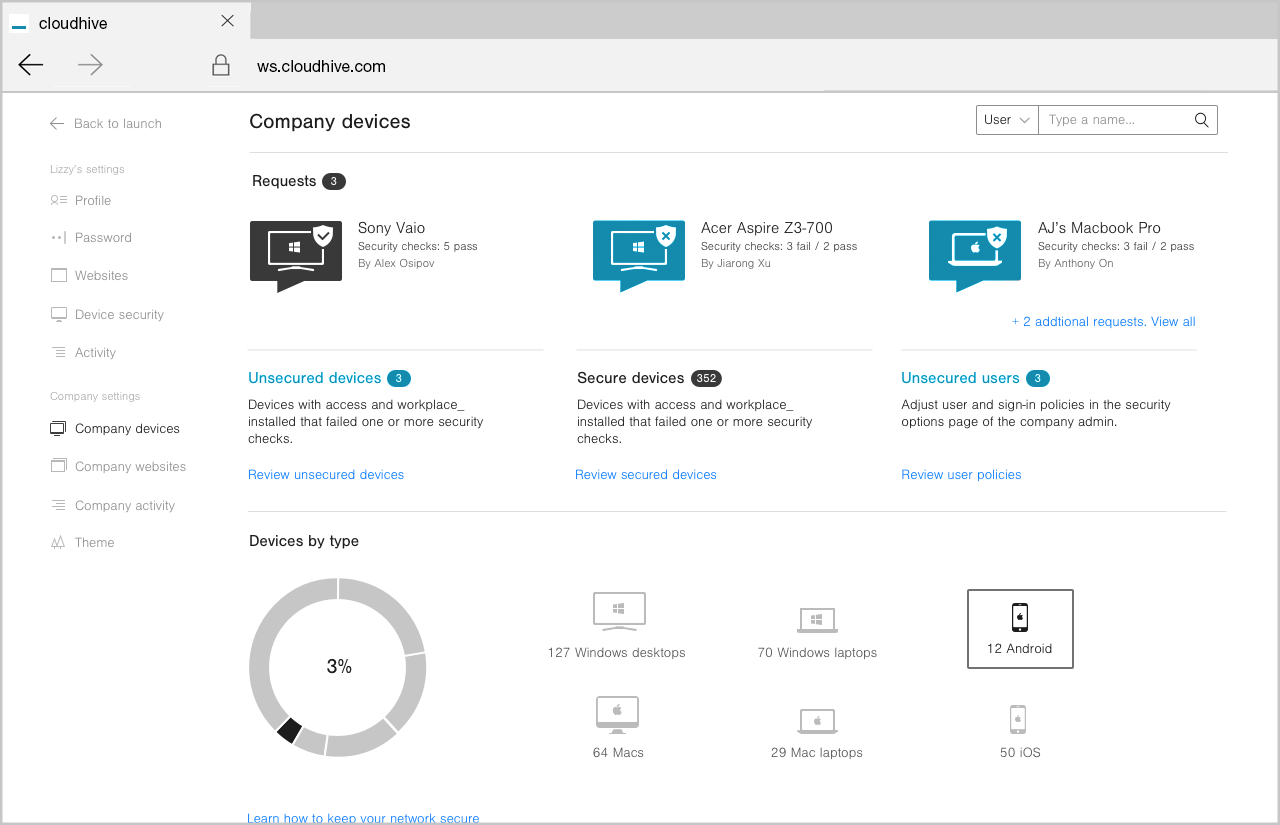
It’s simple to approve access, and just as simple to disengage that access
Once end-users are approved for access they are given login credentials to their own unique webtop. This makes it simple for them to be able to work with all the files, folders, approved apps and legacy software that they have been given permission to access.
They can personalise their webtop, organise programs, post announcements and share shortcuts.
When an end-user has no further requirement to have access to the company files then your company Administrator can disengage the individual’s webtop and access to all applications immediately.
.